Why Need to Detect MySQL Brute-force Password Attacks?
MySQL brute-force password attacks are the act of attempting to illegally gain access to a MySQL database. These attempts will systematically try various possible passwords.
The harm of MySQL password brute-force attack includes the following:
- Data Leakage: Successful attacks may lead to the exposure of sensitive information stored in the database, such as user personal data, financial information, etc., resulting in data leakage.
- Service Disruption: The extensive password attempts can overload the database server. And they will ultimately cause the server to crash or become unavailable, leading to service disruption.
- Account Compromise: Successful password compromises may result in attackers taking control of database accounts. Then they will be allowed to execute unauthorized actions such as tampering with data, deleting data, etc.
- Reputation Damage: Database breaches can severely damage an organization’s reputation and trust. These damages potentially result in customer loss and legal liabilities.
- Secondary Attacks: Password brute-force attacks may be part of broader attack campaigns, such as data ransom, social engineering attacks, etc.
These harms can have serious implications for organizations. They also highlight the importance to early prevent and detect MySQL password brute-force attacks.
Detect MySQL Brute-force Pssword Attacks by Unicorn [Easy and Reliable]
Unicorn is a professional network threat analysis tool that comes with MySQL password brute-force detection rules. It is very easy to detect this type of network threat.
Step 1. Just launch the application and click the “Start” button.
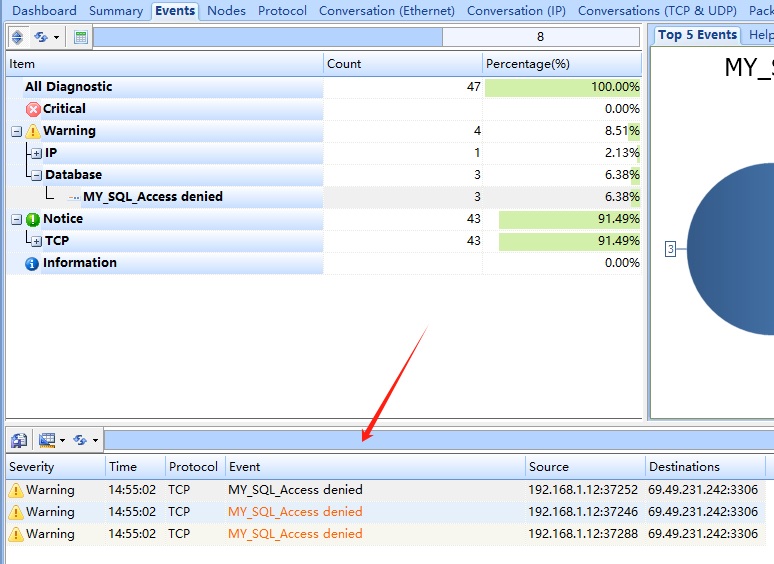
Step 2. At this point, if we initiate a simulated attack, we can see a large number of “MYSQL_Access denied” events, as shown in the image below:
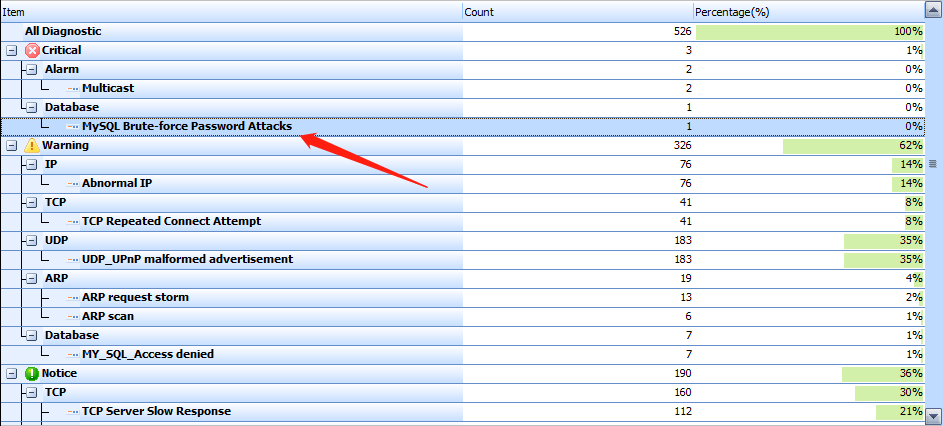
Step 2. If the number of detected events exceeds the set threshold, Unicohen will trigger “MySQL Brute-force Password Attacks” event, as shown in the image below:
How to Prevent MySQL Brute-Force Password Attacks
Detecting MySQL password brute-force attacks can be achieved through the following methods:
- Failure Login Attempt Logs: Monitor MySQL logs to detect frequent failed login attempts. A large number of failed login attempts, especially from the same IP address or user, may indicate someone is attempting to brute-force passwords.
- Use of Intrusion Detection Systems (IDS/IPS): Deploy intrusion detection systems like Unicorn to monitor network traffic on database servers. IDS/IPS can detect abnormal login patterns and frequent password attempts. So, they can perfectly identify potential password brute-force attack.
- Limit Login Attempt Times: Utilize MySQL’s security configuration parameters to restrict the number of login attempts allowed for a single IP address or user within a certain period. Login attempts exceeding the limit should be denied or temporarily lock the account.
- Implement Strong Password Policies: Enforce the usage of strong passwords for database users and regularly change passwords. Strong passwords can increase the difficulty of password brute-force attacks.
- Real-time Monitoring and Response: Use real-time monitoring tools to detect abnormal activities on database servers and take immediate response measures, such as blocking attacker IP addresses or temporarily disabling affected accounts.
- Encrypted Connections: Ensure that connections to the MySQL database are encrypted, such as using SSL/TLS encryption to protect passwords during transmission.
Conclusion
By implementing these measures, MySQL password brute-force attacks can be detected and prevented in a timely manner, thus enhancing the security of the database.