Global Variable sigmatch_table
typedef struct SigTableElmt_ {
/** Packet match function pointer */
int (*Match)(DetectEngineThreadCtx *, Packet *, const Signature *, const SigMatchCtx *);
/** InspectionBuffer transformation callback */
void (*Transform)(InspectionBuffer *, void *context);
bool (*TransformValidate)(const uint8_t *content, uint16_t content_len, void *context);
/** keyword setup function pointer */
int (*Setup)(DetectEngineCtx *, Signature *, const char *);
void (*Free)(DetectEngineCtx *, void *);
uint16_t flags;
/* coccinelle: SigTableElmt:flags:SIGMATCH_ */
const char *name; /**< keyword name alias */
const char *alias; /**< name alias */
const char *desc;
const char *url;
} SigTableElmt;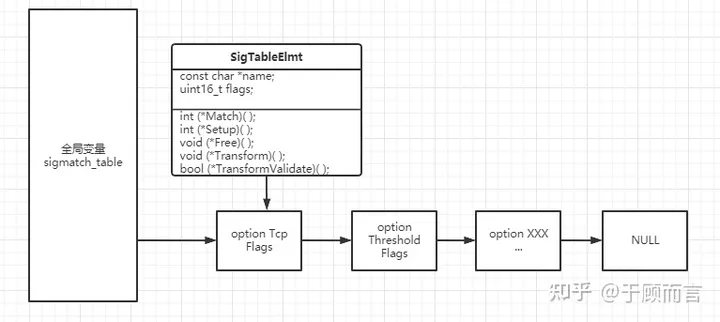
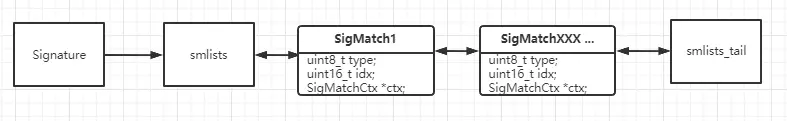
Bidirectional Linked List of Options in Rules
enum DetectSigmatchListEnum {
DETECT_SM_LIST_MATCH = 0,
DETECT_SM_LIST_PMATCH,
/* base64_data keyword uses some hardcoded logic so consider
* built-in
* TODO convert to inspect engine */
DETECT_SM_LIST_BASE64_DATA,
/* list for post match actions: flowbit set, flowint increment, etc */
DETECT_SM_LIST_POSTMATCH,
DETECT_SM_LIST_TMATCH, /**< post-detection tagging */
/* lists for alert thresholding and suppression */
DETECT_SM_LIST_SUPPRESS,
DETECT_SM_LIST_THRESHOLD,
DETECT_SM_LIST_MAX,
/* start of dynamically registered lists */
DETECT_SM_LIST_DYNAMIC_START = DETECT_SM_LIST_MAX,
};
General Option Process
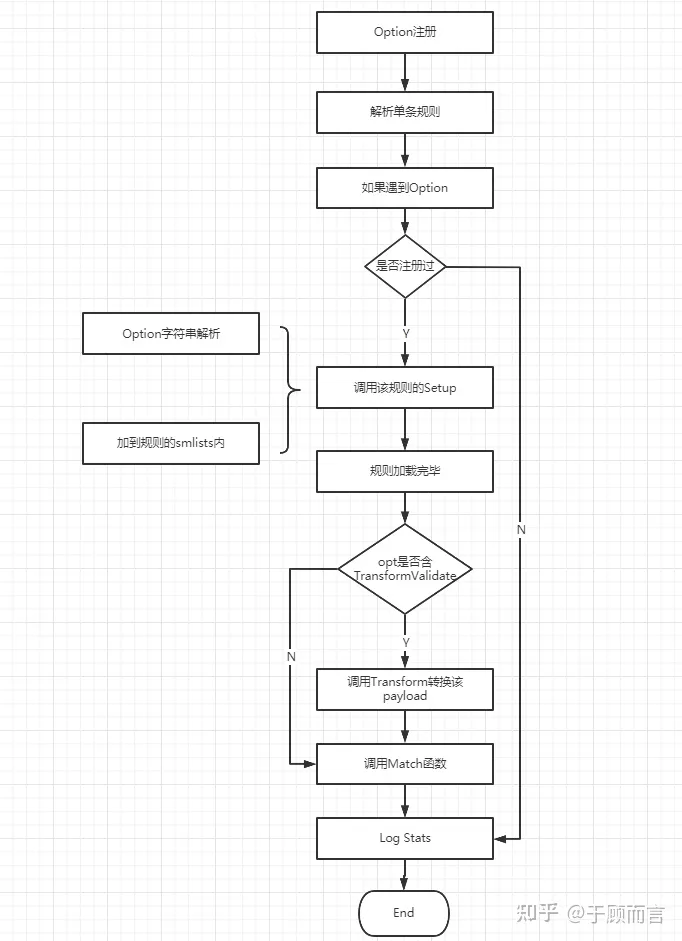
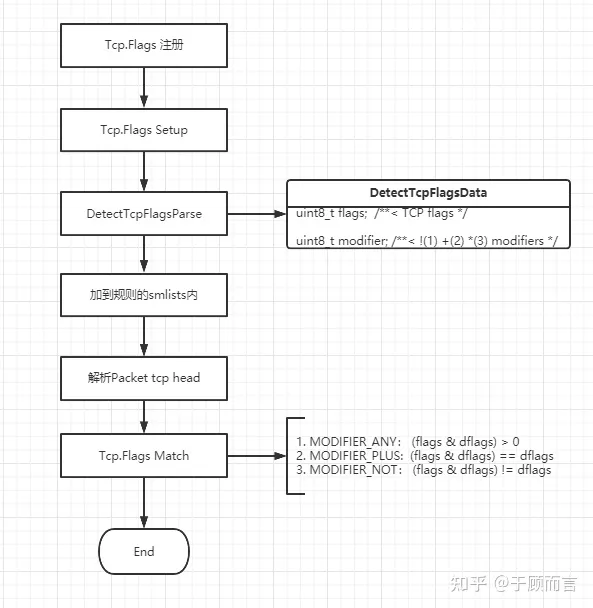
Tcp.Flags
Example of rule:
alert tcp $EXTERNAL_NET any -> $HOME_NET any (msg:"GPL SCAN nmap fingerprint attempt"; flags:SFPU; flow:stateless; reference:arachnids,05; classtype:attempted-recon; sid:2100629; rev:7; metadata:created_at 2010_09_23, updated_at 2010_09_23;)Implementation flowchart:
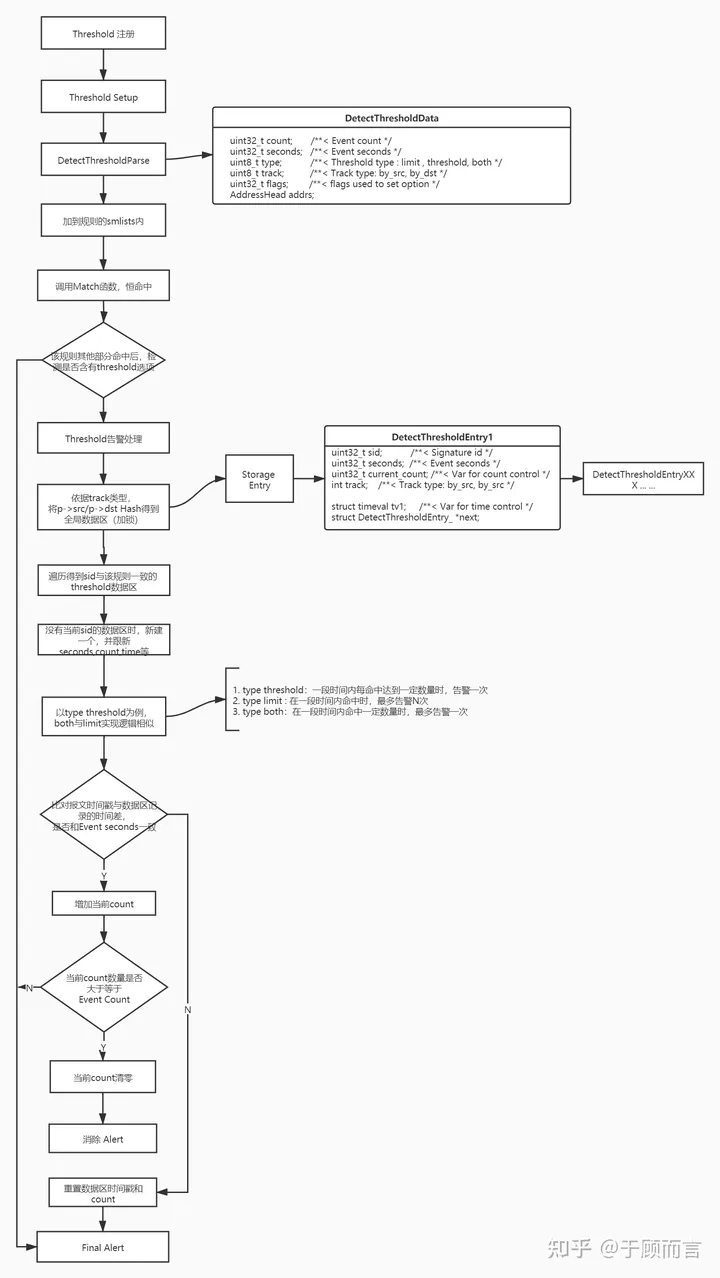
Threshold
Example of rule:
alert tcp $EXTERNAL_NET 10000: -> $HOME_NET 0:1023 (msg:"ET DOS Potential Tsunami SYN Flood Denial Of Service Attempt"; flags:S; flow:to_server; dsize:>900; threshold: type limit, count 20, seconds 120, track by_src; classtype:attempted-dos; sid:2019404; rev:3; metadata:created_at 2014_10_15, updated_at 2014_10_15;)Implementation flowchart: